Europol has supported the coordination of a large-scale international operation that has taken down the infrastructure of the Qakbot malware and led to the seizure of nearly EUR 8 million in cryptocurrencies. The international investigation, also supported by Eurojust, involved judicial and law enforcement authorities from France, Germany, Latvia, The Netherlands, Romania, United Kingdom and the United States. Qakbot, operated by a group of organised cybercriminals, targeted critical infrastructure and businesses across multiple countries, stealing financial data and login credentials. Cybercriminals used this persistent malware to commit ransomware, fraud, and other cyber-enabled crimes.
Active since 2007, this prolific malware (also known as QBot or Pinkslipbot) evolved over time using different techniques to infect users and compromise systems. Qakbot infiltrated victims’ computers through spam emails containing malicious attachments or hyperlinks. Once installed on the targeted computer, the malware allowed for infections with next-stage payloads such as ransomware. Additionally, the infected computer became part of a botnet (a network of compromised computers) controlled simultaneously by the cybercriminals, usually without the knowledge of the victims. However, Qakbot’s primary focus was on stealing financial data and login credentials from web browsers.
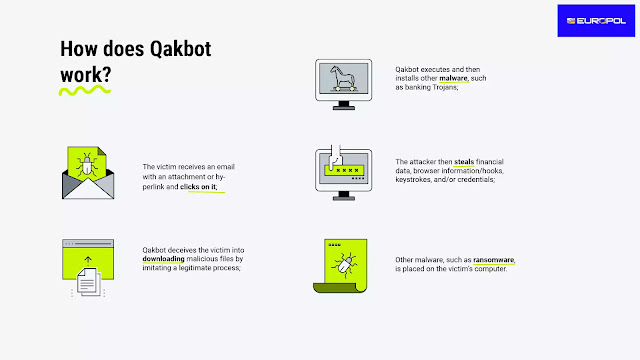
How does Qakbot work?
The victim receives an email with an attachment or hyperlink and clicks on it;
Qakbot deceives the victim into downloading malicious files by imitating a legitimate process;
Qakbot executes and then installs other malware, such as banking Trojans;
The attacker then steals financial data, browser information/hooks, keystrokes, and/or credentials;
Other malware, such as ransomware, is placed on the victim’s computer.
Over 700 000 infected computers worldwide
A number of ransomware groups used Qakbot to carry out a large number of ransomware attacks on critical infrastructure and businesses. The administrators of the botnet provided these groups with access to the infected networks for a fee. The investigation suggests that between October 2021 and April 2023, the administrators have received fees corresponding to nearly EUR 54 million in ransoms paid by the victims. The lawful examination of the seized infrastructure uncovered that the malware had infected over 700 000 computers worldwide. Law enforcement detected servers infected with Qakbot in almost 30 countries in Europe, South and North America, Asia and Africa, enabling the malware’s activity on a global scale.
Over the course of the investigation, Europol facilitated the information exchange between participating agencies, supported the coordination of operational activities, and funded operational meetings. Europol also provided analytical support linking available data to various criminal cases within and outside the EU. The Joint Cybercrime Action Taskforce (J-CAT) at Europol also supported the operation. This standing operational team consists of cybercrime liaison officers from different countries who work on high-profile cybercrime investigations.
Eurojust actively facilitated the cross-border judicial cooperation between the national authorities involved. The Agency hosted a coordination meeting in July 2023 to facilitate evidence sharing and to prepare for this joint operation.
Law enforcement authorities involved:
France: National Police (Police Nationale) and National Gendarmerie (Gendarmerie Nationale)
Germany: Federal Criminal Police Office (Bundeskriminalamt)
Latvia: State Police (Valsts policija)
The Netherlands: National Police (Politie)
Romania: Romanian Police (Poliția Română)
United Kingdom: National Crime Agency
United States: Federal Bureau of Investigation (US FBI)
Judicial authorities involved:
France: National Jurisdiction against Organised Crime (JUNALCO), Public Prosecutor’s Office Cybercrime Unit;
Germany: Prosecutor General's Office Frankfurt am Main – Cyber Crime Centre;
The Netherlands: National Public Prosecutor’s Office Rotterdam
United States: US Attorney’s Office for the Central District of California and the Department of Justice’s Computer Crime and Intellectual Property Section
Commenti
Posta un commento